A Structural Model for Preventing Layered Risk Alignment in Public Systems
Executive Summary
Public sector failures rarely originate from a single error. They emerge when small, unaddressed weaknesses align across multiple layers of governance. These weaknesses often exist in plain sight. Policies are documented, risks are logged, audits are completed, training is delivered, and performance indicators remain within tolerance. Yet failure still occurs.
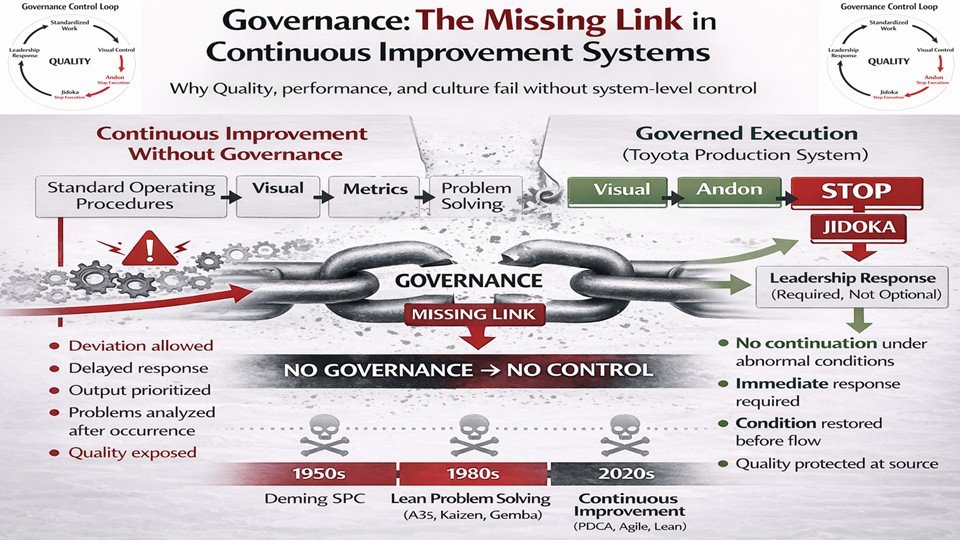
The issue is not the absence of oversight. It is the absence of structural verification.
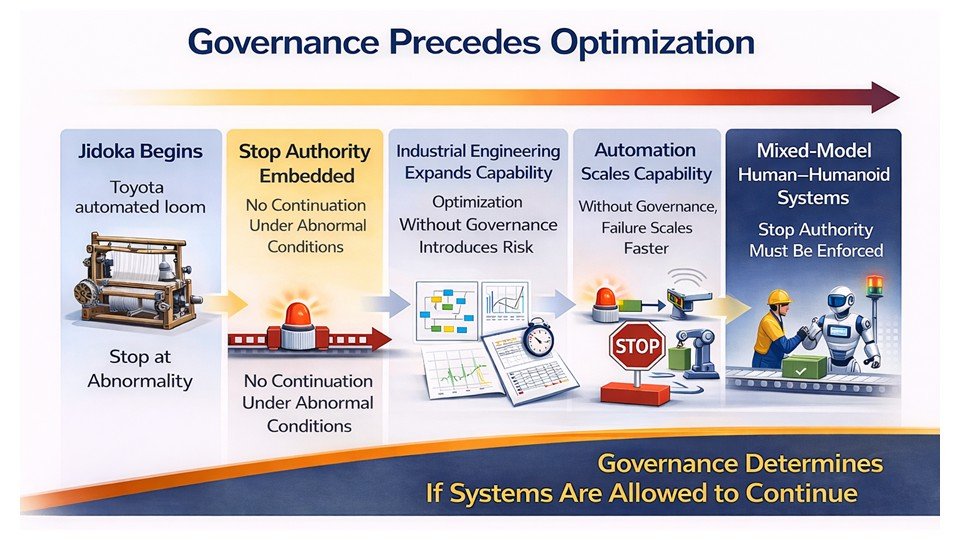
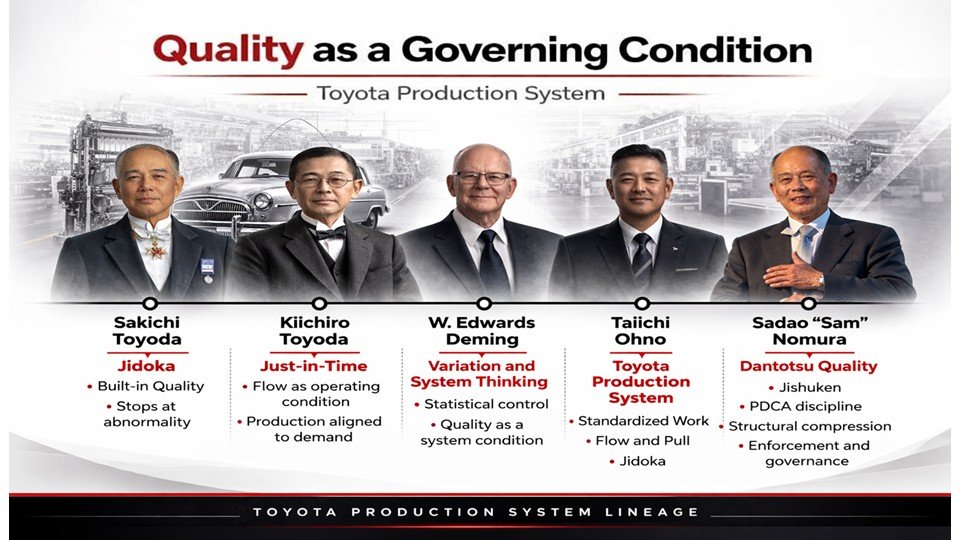
Modern government risk systems rely heavily on administrative assurance. Documentation substitutes for observation, risk registers substitute for flow analysis, audit cycles substitute for real-time verification, and compliance substitutes for learning. These mechanisms confirm that governance artifacts exist, but they do not ensure that protective layers remain structurally intact. As a result, risk is recorded but not prevented, and Quality gradually shifts from a governing condition to a reported outcome.
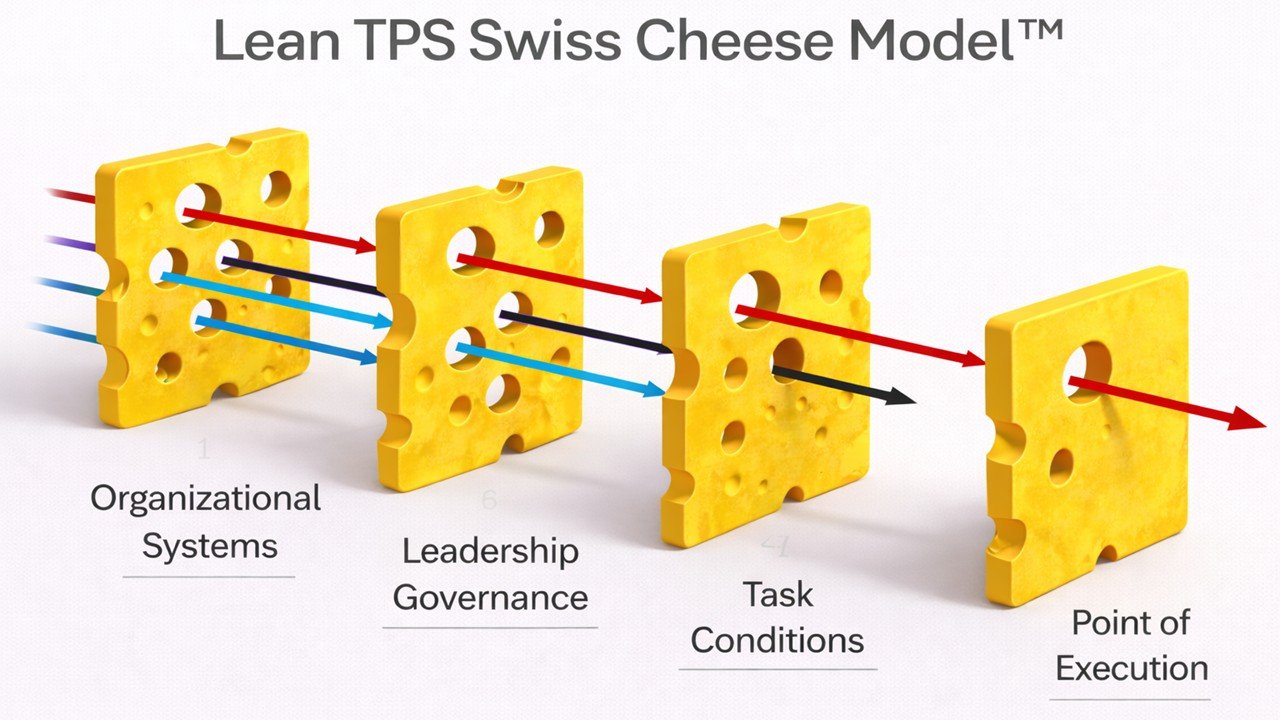
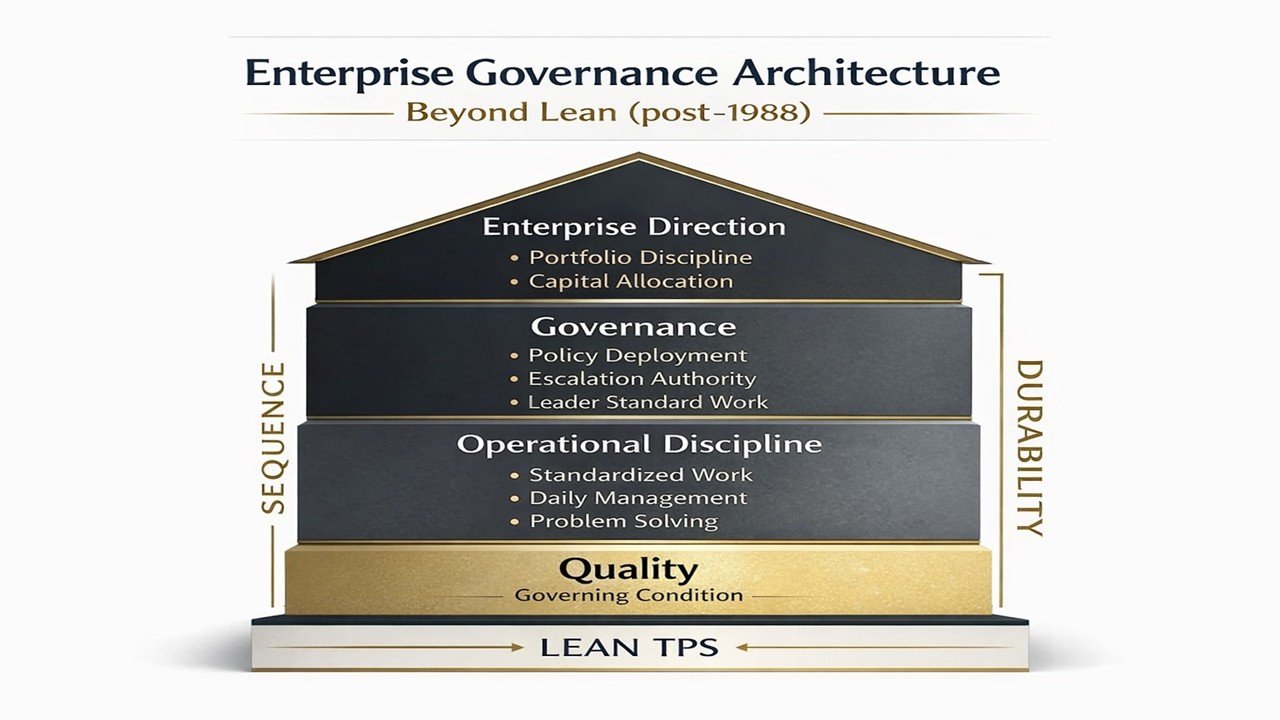
This paper introduces the Swiss Cheese Governance Architecture – Government Edition, a structural model for understanding how layered risk alignment forms and how it can be prevented. The model identifies four interdependent protective governance layers: organizational systems, leadership governance, task conditions and human factors, and active failure at the point of execution. Each layer is designed to interrupt instability before it moves downstream. When one layer weakens, risk begins to travel. When multiple layers weaken simultaneously, small vulnerabilities align into visible system failure.
Public sector reviews frequently concentrate on the final event. Investigations examine the visible breakdown at the frontline and assess compliance with procedure. However, that breakdown is typically the final expression of deeper structural drift. Failures are not sudden disruptions; they are aligned outcomes of weakened feedback between layers.
Government governance frameworks often measure compliance rather than condition. They confirm whether procedures were followed, whether documentation was complete, and whether controls were formally in place. They rarely verify whether operating conditions remained stable, whether leadership presence was structurally embedded, or whether weak signals were escalated early. Without embedded verification, protective layers appear intact while operational instability accumulates.
The Swiss Cheese Governance Architecture reframes prevention as structural control rather than administrative validation. It shifts attention from post-event review to upstream design. Effective prevention requires clearly defined normal operating conditions, visible flow across departmental boundaries, structured leadership presence that verifies real conditions, unambiguous escalation logic when abnormality appears, and embedded learning that modifies system design. Governance must operate at operational tempo rather than audit tempo if it is to preserve Quality as a governing condition.
This white paper examines common structural failure modes in public systems, including overreliance on documentation, KPI dashboards detached from flow reality, corrective action cycles without architectural redesign, and risk registers disconnected from daily execution. It then presents a counter-architecture that embeds visibility, escalation, and learning directly into governance design so that deviation is detected and interrupted before alignment occurs.
The central thesis is direct. Failures align when governance layers lose structural feedback. Prevention requires architecture rather than paperwork.
The Swiss Cheese Governance Architecture provides public leaders with a disciplined framework to diagnose layered drift, reinforce protective layers, and prevent small weaknesses from aligning into system-wide failure. By restoring feedback integrity across governance layers, public institutions can protect Quality not as a retrospective metric, but as a continuously verified condition of service delivery.
2. The Governance Problem in Public Systems
Public sector governance has become increasingly sophisticated in documentation while progressively distancing itself from operational reality. Over the past two decades, governments have strengthened oversight frameworks and expanded risk management infrastructure. Risk registers are standardized, audit functions are independent, performance dashboards are digitized, corrective action systems are institutionalized, and compliance reporting is more transparent than ever. Administrative oversight has matured.
Yet systemic failures continue.
Major incidents across public health, infrastructure, procurement, regulatory enforcement, and social services reveal a recurring pattern. The failure was rarely unknown. Signals existed, reports were filed, warnings were raised, and documentation was complete. Despite this, the system did not prevent alignment across governance layers. The issue was not the absence of policy. It was the inability of governance structures to detect and interrupt drift before Quality deteriorated.
The structural problem is not negligence. It is governance design.
Most public risk systems are constructed around administrative assurance rather than operational verification. They confirm that procedures exist, that reviews occurred, and that required controls were documented. They do not continuously verify whether operating conditions remain stable, whether leadership presence is structurally embedded in daily execution, or whether weak signals are escalated in real time. Compliance is validated, but condition is not.
When governance emphasizes artifact validation over condition verification, risk becomes abstract. It is rated rather than traced through workflow, reviewed rather than observed in context, and discussed rather than structurally interrupted. Governance shifts from protecting Quality at the point of work to confirming that documentation reflects intended control.
This dynamic creates a false sense of stability. Systems may appear compliant while operational instability accumulates beneath the surface. Lagging indicators remain within tolerance even as workload pressure increases and coordination weakens. Reports show adherence while frontline conditions adapt informally to sustain service continuity. Quality erodes gradually, often invisibly, until a triggering event exposes accumulated vulnerability.
Public failures are therefore rarely sudden. They represent the final stage of layered governance drift. Small weaknesses persist within organizational systems. Leadership routines lose verification strength. Task conditions become overloaded or ambiguous. Frontline adaptations compensate quietly to preserve output. Each weakness appears manageable in isolation. Together, they align.
This alignment is seldom visible through periodic oversight mechanisms. Audit cycles operate on scheduled intervals, and performance dashboards reflect aggregated outcomes rather than emerging instability. Risk registers catalogue identified threats but do not necessarily connect them to real-time operational flow. By the time deviation becomes measurable within formal systems, it has already traversed multiple protective layers.
Post-incident reviews predictably conclude that policies were adequate but not consistently enforced, that warning signs were missed, and that coordination failed across departments. These findings describe symptoms of misalignment. They do not address the structural absence of embedded feedback capable of protecting Quality before alignment forms.
The core problem is not the absence of frameworks. It is the absence of structural feedback embedded into daily operations.
Effective prevention requires governance that operates at the tempo of the work itself. It requires visibility across governance layers, defined escalation logic when abnormal conditions appear, and leadership routines that verify operational reality rather than summarized representation. Without these structural elements, protective layers remain formally intact but functionally weakened, and Quality shifts from a governing condition to a retrospective assessment.
The next section defines the four protective governance layers through which risk travels when structural feedback declines and explains how reinforcing those layers restores feedback integrity across the system.
3. The Four Protective Governance Layers
The Swiss Cheese Governance Architecture defines public system protection as a layered structure of governance controls. Each layer exists to interrupt instability before it moves downstream and degrades Quality at the point of service delivery. When these layers function coherently and are reinforced through structural feedback, they create resilience. When feedback weakens, risk travels silently across layers until visible failure emerges.
The model identifies four interdependent protective governance layers: organizational systems, leadership governance, task conditions and human factors, and active failure at the point of execution. The strength of the system depends not only on the integrity of each layer, but on the clarity and reliability of feedback between them.
3.1 Organizational Systems
The first protective layer consists of the formal structures that define how public work is organized, coordinated, and verified. This includes policy frameworks, process architecture, interdepartmental handoffs, reporting channels, escalation pathways, and clearly defined ownership of responsibilities. Organizational systems determine how work is intended to flow and how Quality is designed to be protected within that flow.
When organizational systems are coherent, responsibilities are explicit, dependencies are visible, and handoffs are structured to prevent loss of information or accountability. Escalation pathways are predefined, and performance measures reinforce system stability rather than local optimization. Under these conditions, deviation from the defined operating state becomes detectable early.
When organizational systems fragment, ambiguity increases. Weak handoffs allow problems to pass between departments without clear ownership. Misaligned performance measures encourage siloed efficiency at the expense of system integrity. Policies may remain formally intact while operational reality evolves informally. Standards become outdated, documentation lags behind practice, and information systems no longer reflect actual workflow.
Failures rarely begin with visible breakdown. They begin when foundational structures drift from operational reality. The system continues to operate, but it no longer operates as designed. Organizational systems must therefore be continuously verified against real conditions if they are to preserve Quality as a governing condition rather than a stated intention.
3.2 Leadership Governance
The second protective layer consists of leadership routines that verify system health and reinforce structural integrity. Governance is not exercised through policy approval alone. It is exercised through disciplined presence, defined escalation logic, and direct confirmation of operational conditions.
Leadership governance determines whether instability is detected early or discovered only after visible harm occurs.
When leaders rely exclusively on summarized reports, dashboards, or periodic reviews, they govern representation rather than condition. Information is filtered as it moves upward, and weak signals lose urgency or context. By the time leadership attention is engaged, instability may have progressed across multiple layers.
Effective governance requires structured cadence. Leaders must verify that documented standards reflect actual work, confirm that escalation pathways function as intended, and respond immediately when abnormal conditions appear. Escalation authority must be unambiguous so that detection produces interruption rather than delay.
Leadership governance either strengthens the protective barrier or becomes another permeable layer. When leadership presence is structural rather than discretionary, Quality remains anchored in operational reality rather than measured retrospectively.
3.3 Task Conditions and Human Factors
The third protective layer represents the environment in which public service work is performed. It includes workload distribution, clarity of expectations, availability of resources, system usability, communication channels, and coordination at the operational level. This layer determines whether the system supports reliability or depends on individual endurance to compensate for design gaps.
Public systems frequently operate under constraint. Staff manage competing priorities, evolving directives, and incomplete information. When workload exceeds capacity or responsibilities lack clarity, individuals adapt to sustain output. These adaptations may preserve short-term continuity, but they gradually normalize deviation from intended design.
The gap between work-as-designed and work-as-performed widens.
When task conditions are unstable, even capable personnel cannot reliably protect Quality. Small adjustments accumulate, protective margins narrow, and reliance on individual vigilance increases. The system continues to function, but its tolerance for disruption declines. Variability becomes embedded rather than corrected.
Stable task conditions reduce dependence on heroics and increase predictability. Structural clarity at this layer reinforces upstream governance. Without it, even strong policy frameworks and leadership oversight cannot compensate for operational instability.
3.4 Active Failure at the Point of Execution
The fourth protective layer is where visible breakdown occurs. This may take the form of service interruption, regulatory failure, financial mismanagement, safety incident, or harm to citizens. At this stage, failure appears discrete and immediate.
Investigations commonly focus on the triggering event by examining individual decisions, procedural adherence, or isolated errors. However, active failure is rarely the origin. It is the final expression of layered drift.
When weaknesses in organizational systems, leadership governance, and task conditions align, protective barriers narrow. A single triggering condition exposes accumulated vulnerability. What appears sudden is structural in origin.
Blame directed solely at the point of execution obscures upstream design weaknesses. Correction limited to the visible event leaves alignment pathways intact. The point of execution reveals what the system has built over time.
3.5 Layer Interaction and Risk Travel
These four layers do not operate independently. They function as interlocking protective barriers through which risk travels when feedback weakens.
When structural clarity declines at the organizational level, leadership visibility diminishes. When leadership verification weakens, task instability increases. When task instability grows, frontline error becomes more probable. Risk moves through openings across layers until it reaches the point of execution.
The Swiss Cheese Governance Architecture does not assign fault to any single layer. It makes visible how layered drift accumulates and how Quality erodes when feedback between layers is insufficient. Prevention requires reinforcing structural feedback across all layers simultaneously. Strengthening one layer in isolation merely redistributes vulnerability.
The next section examines how modern public governance systems unintentionally substitute administrative assurance for structural control, allowing layered drift to continue despite formal compliance.
4. Administrative Substitutions for Structural Control
Modern public governance systems rarely lack formal policy, oversight mechanisms, or compliance frameworks. In many jurisdictions, administrative controls have expanded significantly over the past two decades. Risk registers are standardized, audit regimes are formalized, performance dashboards are digitized, and corrective action processes are codified. Oversight infrastructure is extensive and professionally maintained.
Despite this administrative maturity, systemic failures persist.
The structural problem is not the absence of control. It is substitution. Administrative mechanisms increasingly substitute for structural verification. These substitutions create the appearance of governance strength while allowing layered drift to continue beneath formal compliance. They validate artifacts of governance without verifying whether Quality remains protected within daily operations.
Six substitution patterns recur across public systems.
4.1 Documentation as Assurance
Documentation is indispensable for transparency, accountability, and institutional memory. However, documentation becomes a structural weakness when its existence is treated as evidence of control. Policies may be current, procedures updated, and frameworks formally approved, yet documentation confirms intent rather than condition. It does not verify whether execution remains aligned with design or whether Quality is being protected at the point of work.
When documentation becomes the primary indicator of governance strength, the system shifts from condition verification to record validation. The governing question changes from whether the operating state is stable to whether prescribed steps were followed. Post-incident reviews frequently conclude that policies were adequate but inconsistently applied. This recurring conclusion reflects a structural gap between documented architecture and operational reality. The presence of policy did not prevent layered alignment because policy was not continuously verified against execution.
Documentation can describe governance. It cannot substitute for structural feedback.
4.2 Risk Registers Detached from Operational Flow
Risk registers catalogue threats, assess likelihood, and assign mitigation strategies. They provide strategic visibility and formal traceability. However, they often remain detached from the operational flow where instability actually forms.
A risk may be logged, rated, and reviewed periodically. It may be formally classified as controlled. Yet mitigation actions are rarely embedded into daily routines in a manner that triggers interruption when abnormal conditions appear. Escalation logic may exist administratively without activating at operational tempo.
This separation produces structural vulnerability. Risk awareness exists at the strategic level, but detection and interruption mechanisms are not integrated into workflow. When failure occurs, review often reveals that the risk had been previously identified. The weakness was known. It was not structurally connected to mechanisms capable of protecting Quality in real time.
Risk recorded is not risk controlled.
4.3 Audit Without Real-Time Verification
Audit systems confirm compliance with established frameworks and test whether documented controls were followed during defined review periods. They provide critical accountability and assurance functions.
However, audit operates episodically. It reviews past conditions and validates discrete snapshots. Governance drift occurs continuously.
Between audit cycles, workload levels change, task conditions evolve, coordination patterns shift, and informal adaptations emerge to maintain service continuity. These changes rarely surface until measurable deviation appears or visible harm occurs. By that stage, instability may have already progressed across multiple protective layers.
Audit confirms that governance structures existed. It does not confirm that those structures remained functionally protective under dynamic conditions. Oversight conducted at audit tempo cannot replace verification conducted at operational tempo.
4.4 KPI Reliance and Lagging Visibility
Performance dashboards and KPIs provide measurable outcome indicators and enable comparison across departments and programs. They are essential instruments of accountability. However, most KPI systems rely predominantly on lagging indicators that confirm what has already occurred.
Lagging indicators do not detect emerging instability.
When dashboards remain within tolerance, leadership often assumes stability. Yet early signals may already be present within task conditions, including increased workarounds, rising workload strain, delayed handoffs, and growing ambiguity in responsibility. These signals rarely appear immediately in aggregated metrics because metrics are designed to measure outcomes rather than protective condition.
The absence of red indicators is frequently interpreted as proof of control. In reality, metrics may simply trail structural drift. KPI systems measure results. They do not automatically verify whether the conditions that protect Quality remain intact.
4.5 Training Without Structural Reinforcement
Training initiatives are commonly deployed following incidents or audit findings. Staff receive updated instruction, certifications are renewed, and awareness campaigns are launched. These efforts are often well-designed and professionally delivered.
However, training alone does not alter structural conditions.
If workload imbalance, flawed process design, escalation ambiguity, or system usability constraints remain unchanged, personnel will revert to adaptation under pressure. Knowledge decays without reinforcement, and skills degrade without structural integration into daily routines. When recurrence occurs, analysis frequently centers on individual compliance rather than on the design conditions that made deviation likely.
Capability cannot be sustained without structural reinforcement. Quality cannot be protected through instruction alone when operating conditions remain unstable.
4.6 Corrective Action Closure Without Redesign
Corrective action processes are intended to strengthen governance by identifying root causes and assigning countermeasures. Findings are documented, action plans are tracked, and completion is verified.
However, closure frequently becomes the primary objective. Once actions are marked complete and reports submitted, the issue is considered resolved. If the underlying architecture remains unchanged, the same vulnerability persists under a new tracking number.
The organization demonstrates procedural responsiveness without structural transformation. When recurrence occurs, it appears as a new incident rather than continuation of an unresolved alignment pathway. Corrective action without redesign stabilizes documentation but does not necessarily reinforce governance layers or protect Quality upstream.
4.7 Structural Consequence of Substitution
Each substitution pattern shares a common characteristic. It validates governance artifacts rather than verifying operational condition. Documentation confirms that rules exist. Registers confirm that risks are catalogued. Audits confirm that frameworks were followed. KPIs confirm that outcomes remain within tolerance. Training confirms that knowledge was delivered. Corrective action confirms that responses were recorded.
None of these mechanisms, in isolation, ensure that protective layers remain structurally intact or that Quality is protected at the point of execution.
When administrative assurance replaces structural verification, risk travels silently across governance layers. By the time visible breakdown occurs, every substitution mechanism may still appear compliant.
The next section examines why this drift persists and how structural distance between policy and execution accelerates layered alignment.
5. Why Government Governance Drifts
Administrative substitution does not occur accidentally. It emerges from structural characteristics common to large public systems. Governance drift is rarely a failure of intent or effort. It is a predictable outcome of how oversight is organized, how information is filtered, and how leadership verifies system condition.
Several reinforcing structural dynamics gradually weaken protective layers and accelerate layered drift.
5.1 Distance Between Policy and Execution
Public systems are typically organized hierarchically and functionally, with policy development, oversight, and frontline execution operating at different levels and often separated by multiple management layers. As structural distance increases, abstraction increases.
Policy is formulated at a strategic level. Execution occurs under operational constraints that evolve daily. Over time, work adapts to real-world conditions that were not fully anticipated in original design. Informal adjustments accumulate in order to sustain service continuity and meet performance expectations. These adaptations are rarely transmitted upward in structured or timely form.
The result is a widening gap between work-as-designed and work-as-performed.
When governance relies primarily on summarized reporting rather than direct verification of operating conditions, leadership awareness of this gap diminishes. Policies appear effective because they are reviewed administratively and formally endorsed. Meanwhile, execution compensates silently for design weaknesses that remain structurally unaddressed. Quality becomes dependent on individual vigilance rather than system stability.
Distance reduces feedback fidelity. Reduced feedback fidelity permits drift.
5.2 Governance Through Abstraction
Large public systems depend on aggregated reporting to manage scale and complexity. Metrics are consolidated, risk ratings standardized, and exceptions categorized before reaching senior decision-makers. This abstraction is operationally necessary. However, abstraction filters variation.
Weak signals typically originate in qualitative observations, operational friction, boundary delays, or informal workarounds. These signals are seldom preserved in aggregate reporting. They are normalized as local irregularities rather than interpreted as structural warnings. As information moves upward through layers of reporting, context erodes and urgency diminishes.
Over time, governance shifts from condition-based awareness to representation-based awareness. Leaders govern dashboards rather than system health. Reports may convey stability while instability accumulates within task conditions.
When abstraction replaces observation, Quality becomes a reported outcome rather than a continuously verified condition.
5.3 Oversight at Audit Tempo Rather Than Operational Tempo
Audit and formal review cycles typically operate quarterly, semi-annually, or annually. Strategic reassessment may occur even less frequently. Operational systems, by contrast, evolve continuously.
Workloads fluctuate, directives shift, personnel change, technology platforms update, and workarounds emerge to absorb pressure. These changes affect system stability long before they appear in formal review cycles.
When governance operates at a slower tempo than operational change, verification lags behind variation. Drift accumulates between review intervals. By the time deviation becomes measurable within formal oversight structures, it may have already traversed multiple protective layers.
Oversight conducted at audit tempo cannot reliably protect Quality in systems that evolve daily.
5.4 Escalation Ambiguity
Protective governance systems require clear escalation logic. When abnormal conditions appear, response authority must be defined, immediate, and understood across layers.
In many public systems, escalation pathways exist formally but function interpretively. Staff may hesitate to elevate concerns due to unclear thresholds, ambiguous ownership, fear of disproportionate reaction, or uncertainty regarding consequences. Escalation becomes discretionary rather than structural.
When escalation depends on judgment rather than predefined triggers, weak signals remain localized. They are absorbed into routine reporting or deferred to scheduled reviews. Detection does not automatically produce interruption.
Interpretive escalation creates permeable protective layers. Risk continues to travel because interruption is not structurally guaranteed.
5.5 Fragmented Flow Across Departments
Public systems frequently operate through distributed and interdependent responsibilities. Service delivery depends on coordination among policy units, operational divisions, regulatory bodies, external partners, and contracted providers. Each unit may meet its individual targets while instability accumulates at boundaries.
When performance measures are optimized locally rather than aligned systemically, vulnerabilities form at handoffs. Delays, information loss, unclear accountability, and duplicated effort concentrate at transition points between departments. These boundary conditions are rarely visible in aggregated reporting and often remain uncorrected until exposed by failure.
Layered governance requires cross-boundary visibility and shared responsibility for Quality. Without it, risk alignment can occur across otherwise compliant units.
5.6 Cultural Normalization of Deviation
Over time, recurring small deviations become accepted as routine. Staff adapt to constraints, compensate for ambiguity, and resolve friction informally in order to maintain continuity. These adaptations often reflect professionalism and commitment. However, they conceal structural weakness.
As deviation becomes normalized, warning signs lose urgency. Tolerance for instability increases incrementally. Each adjustment appears minor in isolation, but collectively they reduce protective margin and increase exposure.
By the time visible failure occurs, deviation has been embedded into daily practice. The system has adapted around instability rather than correcting it.
Drift rarely announces itself. It stabilizes gradually until Quality deteriorates beyond the system’s capacity to absorb variation.
5.7 Structural Pattern of Drift
Governance drift accelerates when policy and execution are separated without structured feedback, when oversight relies on abstraction rather than observation, when verification operates at a slower tempo than operational change, when escalation thresholds are unclear, when departments optimize locally rather than systemically, and when deviation becomes culturally normalized.
Under these conditions, protective layers remain formally intact but functionally weakened. Risk alignment becomes possible not because controls are absent, but because feedback between layers is insufficient to preserve Quality as a governing condition.
The next section introduces a structural counter-architecture designed to restore feedback at operational tempo and reinforce protective layers through embedded verification.
6. Structural Counter-Architecture for Government Governance
If layered risk alignment emerges from weakened feedback between governance layers, prevention requires restoring structural feedback at every level of the system. The Swiss Cheese Governance Architecture does not propose additional documentation, expanded reporting frameworks, or more complex risk scoring models. It proposes a structural shift from administrative assurance to embedded operational verification.
Prevention must operate at the tempo of the work itself.
This counter-architecture rests on five reinforcing structural principles that collectively restore Quality as a governing condition rather than a retrospective metric.
6.1 Defined Normal Operating Condition
Every protective system requires a clearly defined baseline. A normal operating condition must be explicit, measurable, and operationally meaningful. This includes defined process flow, workload expectations, escalation thresholds, decision rights, and ownership at handoffs. When normal is undefined or loosely interpreted, deviation cannot be detected reliably and Quality cannot be protected consistently.
In many public systems, normal is assumed rather than specified. Variation is tolerated until visible harm occurs or performance indicators deteriorate materially. This approach delays intervention and permits instability to accumulate beneath acceptable outcomes.
A defined operating condition makes deviation visible early. It enables the system to distinguish between routine fluctuation and structural drift. Without a defined baseline, drift blends into daily variability and remains undetected until alignment across layers has already formed.
Clarity is not cosmetic. It is structural control. It anchors every protective layer to a shared and verifiable understanding of stability.
6.2 Visible Flow Across Governance Layers
Risk does not move randomly. It travels along workflow pathways, through handoffs, and across departmental boundaries. When flow is invisible, instability accumulates at these transition points without timely interruption.
Governance must make cross-layer flow visible at operational tempo. This includes awareness of backlog growth, handoff delays, exception rates, escalation frequency, coordination breakdowns, and workload imbalance. Visibility must extend beyond aggregate metrics to reveal real operating condition.
When leaders can see where work slows, where rework increases, or where responsibilities become ambiguous, intervention becomes preventive rather than reactive. Abstract risk is converted into observable condition. Quality is no longer inferred from outcome metrics but anchored in the stability of movement across layers.
Visibility transforms governance from periodic review into continuous awareness.
6.3 Structured Leadership Presence
Leadership governance cannot rely exclusively on summarized reporting or formal review cycles. It must include structured and recurring verification of operational conditions at the point of execution. Presence is not symbolic. It is structural.
Structured leadership presence requires routine confirmation that documented standards reflect actual work, that escalation logic functions as intended, that workload aligns with capacity, and that weak signals are surfaced rather than absorbed locally. Verification must occur at operational tempo rather than audit interval.
When leadership presence is embedded rather than discretionary, feedback fidelity increases. Weak signals are elevated earlier. Drift is corrected before alignment across layers becomes possible. Distance filters information and dilutes urgency. Presence restores direct awareness of system condition and reinforces Quality as a governing reality rather than a reported abstraction.
Quality is preserved when leaders verify condition directly.
6.4 Binary Escalation Logic
Protective systems require clear and reliable response triggers. When abnormal conditions appear, the system must either continue under verified stability or escalate immediately according to predefined thresholds. Ambiguity in escalation permits risk to continue traveling across layers.
Binary escalation logic does not imply overreaction. It requires clearly defined thresholds that remove interpretive hesitation. Staff should not debate whether a condition merits attention. The structure must define when escalation occurs and who holds response authority.
When escalation is interpretive, detection does not guarantee interruption. When escalation is structured, interruption becomes automatic. Binary logic reinforces every upstream layer by ensuring that weak signals trigger protective response before deviation compounds.
Escalation clarity protects Quality at the point of detection rather than after consequence.
6.5 Embedded Learning and Structural Redesign
When abnormality is identified, response must extend beyond event correction. The system itself must be examined and, where necessary, redesigned to restore protective margin. Embedded learning requires structured reflection integrated into operational tempo rather than confined to post-incident review.
Countermeasures must modify process design, clarify responsibilities, adjust workload balance, or strengthen escalation thresholds. Updating documentation alone does not rebuild protective capacity. Administrative closure may stabilize records, but it does not reinforce architecture.
Structural systems redesign conditions. Administrative systems close cases.
Without redesign, recurrence remains probable because the alignment pathway remains intact. With redesign, the system strengthens its resistance to layered drift and reinforces Quality as a governing principle rather than a compliance target.
6.6 Reinforcing Layer Integrity
These five structural principles restore feedback across the four protective governance layers. Defined operating condition strengthens organizational systems by aligning design with execution. Visible flow improves cross-layer awareness and exposes instability before it compounds. Structured leadership presence reinforces governance routines and reduces abstraction. Binary escalation protects the point of detection and prevents silent travel. Embedded learning rebuilds protective margin after disruption.
Together, these principles convert governance from periodic review to continuous verification. The objective is not to eliminate variation. Variation is inherent in complex public systems. The objective is to prevent small deviations from aligning across layers and eroding Quality before structural response occurs.
The final section translates this counter-architecture into reform requirements for public institutions and clarifies how structural reinforcement can be embedded without expanding administrative burden.
7. Structural Reform Requirements for Public Systems
The persistence of systemic public failures demonstrates that administrative assurance alone cannot prevent layered risk alignment. Reform cannot rely on procedural expansion, additional reporting, or incremental policy refinement. Reform requires structural redesign that restores feedback across governance layers and protects Quality before instability compounds.
The following governance shifts are necessary to reinforce protective layers and interrupt drift before visible failure emerges.
7.1 Shift from Compliance Validation to Condition Verification
Public oversight systems must move beyond validating that procedures exist and were followed. Governance must verify whether operating conditions remain stable and capable of protecting Quality at the point of execution.
Condition verification requires routine confirmation that process flow remains intact, that workload aligns with capacity, that escalation logic activates when thresholds are reached, and that departmental boundaries do not obscure accountability. Verification must occur at operational tempo rather than solely during scheduled audit cycles.
Compliance confirms adherence to design. Condition verification confirms whether the design continues to function under real-world pressure. Without condition verification, governance remains retrospective and vulnerable to layered drift.
7.2 Embed Leadership Presence into Governance Design
Leadership visibility cannot remain discretionary or symbolic. It must be structurally embedded into governance design as a defined management responsibility.
Senior and mid-level leaders must verify operational conditions directly and regularly. This includes structured observation of workflow, confirmation that escalation pathways function as designed, and direct engagement with frontline execution to detect weak signals early. Governance strengthens when decision-makers observe system condition rather than relying exclusively on summarized representation.
Presence reduces abstraction. Reduced abstraction improves detection. Early detection protects Quality before deviation multiplies across layers.
7.3 Replace Interpretive Escalation with Defined Triggers
Ambiguity in escalation allows risk to travel across governance layers without interruption. Public systems must define clear and operationally meaningful response thresholds for abnormal conditions.
When predefined triggers are reached, escalation must occur automatically and without negotiation or delay. Escalation logic must be visible, understood, and reinforced across all levels of governance. Staff should not rely solely on discretionary judgment to determine whether instability warrants attention.
Defined triggers prevent silent normalization of deviation and ensure that detection produces structural interruption rather than deferred reporting.
7.4 Align Performance Metrics with Flow Stability
Performance measurement systems must extend beyond lagging outcome indicators and incorporate condition-based signals that reveal emerging instability. Metrics should illuminate workload imbalance, backlog growth beyond defined limits, rising escalation frequency, exception rates relative to baseline, and rework concentration at handoffs.
These indicators provide early warning of drift before visible failure or public harm occurs. When performance systems focus exclusively on aggregated outcomes, they confirm historical results but fail to reveal whether protective layers remain intact.
Performance metrics must reinforce structural stability and protect Quality as an operating condition rather than confirm it after deterioration.
7.5 Integrate Risk Management into Operational Flow
Risk identification must connect directly to daily workflow rather than remain confined to strategic documentation. Risk registers must link to real-time verification mechanisms embedded within execution.
When a risk is identified, the system must specify how detection will occur, how escalation will be triggered, and how interruption will be enforced during daily operations. Mitigation strategies must modify process design, clarify roles, or strengthen escalation thresholds rather than remain advisory.
Awareness alone does not prevent alignment. Structural linkage between risk identification and operational verification does.
7.6 Redesign Corrective Action as Structural Learning
Corrective action must extend beyond documentation and closure. Each significant deviation should trigger structured examination of upstream conditions across all governance layers.
Reform requires revisiting system design assumptions, confirming alignment between policy and execution, adjusting escalation thresholds where necessary, and strengthening cross-boundary visibility. Closure without redesign leaves vulnerability intact. Administrative responsiveness does not guarantee structural reinforcement.
Learning must modify architecture if protective margin is to increase. Quality improves when redesign addresses alignment pathways rather than isolated events.
7.7 Reinforce Cross-Layer Visibility
Governance reform must treat protective layers as an integrated architecture rather than isolated functions. Organizational systems, leadership routines, task conditions, and frontline execution must be examined collectively to preserve coherence.
Strengthening one layer without reinforcing adjacent layers merely relocates vulnerability. Cross-layer visibility ensures that improvements in policy, leadership presence, or operational design reinforce one another rather than create new blind spots.
Layer integrity depends on interaction, not isolation.
7.8 Reform as Architectural Discipline
Public systems do not fail because they lack documentation. They fail when documentation substitutes for structural feedback and when abstraction replaces condition verification.
Reform must therefore focus on architecture. It must clarify normal operating conditions, make workflow visible across layers, embed leadership presence into governance routines, define escalation logic unambiguously, and design learning into daily operations. These reforms do not expand administrative burden. They reinforce structural integrity.
The Swiss Cheese Governance Architecture provides a diagnostic and reform framework for identifying weakened protective layers and restoring feedback before layered alignment produces visible failure. By shifting from administrative assurance to embedded operational verification, public institutions can protect Quality as a governing condition and prevent systemic breakdown before it reaches the point of execution.
8. Conclusion
Public failures are rarely sudden events. They are the visible outcome of layered governance drift that has accumulated over time. When protective layers lose structural feedback, small weaknesses align across organizational systems, leadership routines, task conditions, and execution. Administrative assurance may remain formally intact while operational stability and Quality erode gradually beneath the surface.
The persistence of systemic failure does not reflect an absence of frameworks. It reflects a structural gap between administrative validation and operational verification. Policies may be documented, risks catalogued, audits completed, and corrective actions closed. Without embedded feedback operating at operational tempo, these mechanisms cannot prevent alignment across layers.
Prevention requires architecture rather than procedural expansion. Governance must verify condition continuously rather than confirm compliance periodically. Leadership must observe operational reality directly rather than rely exclusively on representation. Escalation must be defined and automatic when abnormal conditions emerge. Learning must redesign system conditions rather than stabilize documentation.
Failures align when feedback weakens between layers. Quality deteriorates when abstraction replaces observation and when escalation becomes interpretive rather than structural.
Strong architecture interrupts alignment. When governance operates at operational tempo, reinforces cross-layer visibility, and protects Quality as a governing condition rather than a reported outcome, layered drift can be detected and corrected before it produces visible harm.
The Swiss Cheese Governance Architecture is not an additional control framework. It is a structural lens for restoring feedback integrity across governance layers. By strengthening that integrity, public institutions can protect Quality at the point of execution and preserve the trust upon which effective government depends.